Leaning on Subject Matter Experts (When You Know Stuff Too)
Being boss doesn't mean you have all the answers, just the brains to recognize the right one when you hear it.” —Katherine Plumber.
How Secure is Secure Enough?
Tl;dr: good practitioners should weigh “enough” security for both technical and business drivers.
Vulnerability Cognition and Communication
This post was guest authored by Nikki Robinson. Vulnerability management is complex. It is, to be blunt, no fun at all. Especially in complex and complicated environments, vulnerability management can feel overwhelming. The sheer volume of vulnerabilities released daily into the National Vulnerability Database (NVD), the scores of vulnerabilities and
Bridging Tarot, Spirituality, and Cybersecurity
This article was a guest post from Caroline Wong. It's uncommon to see the words cybersecurity and tarot used together. So I will ask you to consider that perhaps the intersection exists in the minds of cybersecurity practitioners. Caroline, have you gone completely off the deep end? You
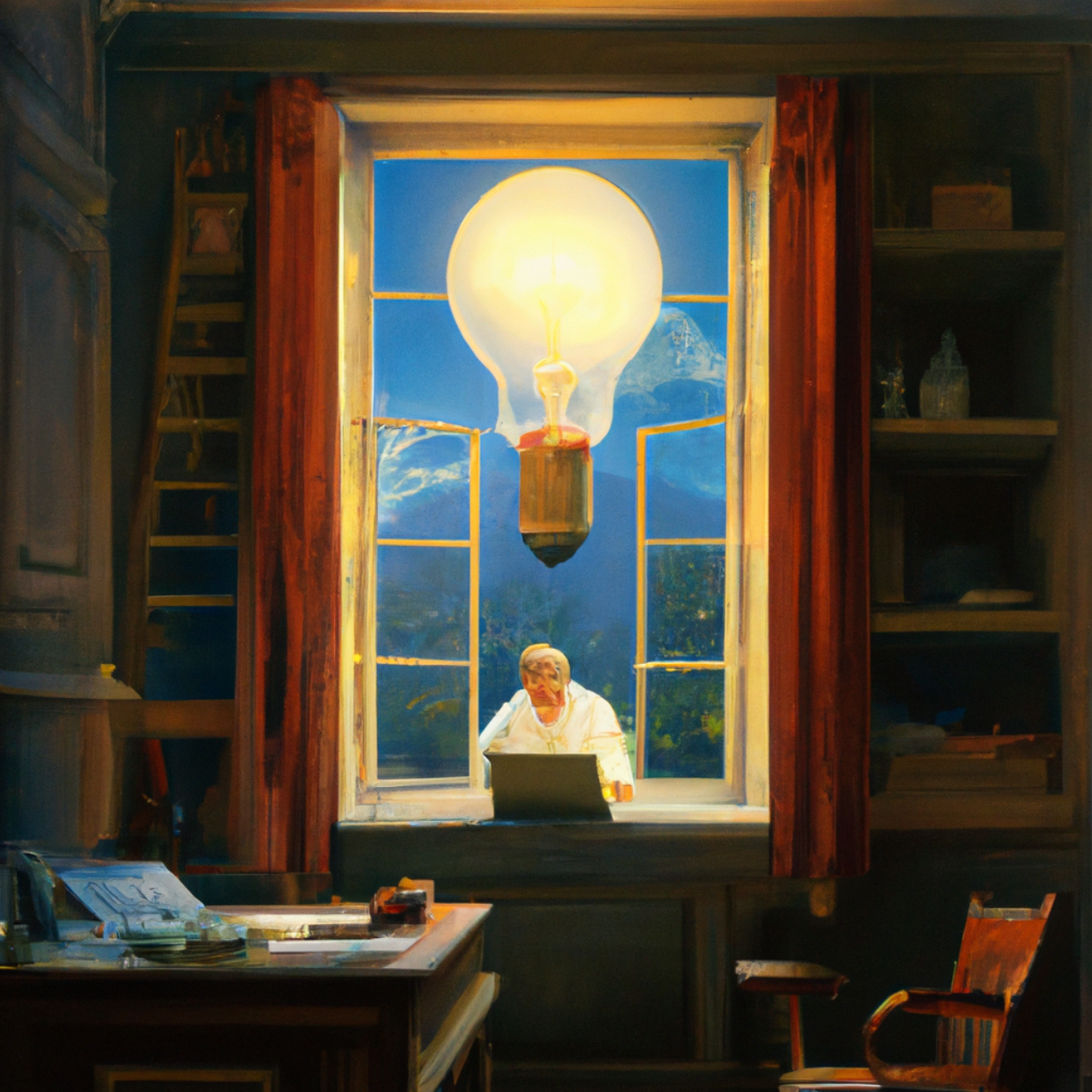
Metacognition: ‘Thinking About the Thinking’ is the Key to Professional Success
This article was a guest post from Jonathan Todd. So you’ve been told you need “soft skills” to succeed in cybersecurity, and you’re probably familiar with some of the most important ones: 1. Empathy: The ability to see a challenge from another’s perspective. 2. Intelligence: The ability
These Shoes Aren't Comfortable
The power of having empathy for our peers