
From Good to Great: The 5 Pillars of a High-Performance Cybersecurity Culture
Cybersecurity culture across an organization is a huge determinant of success or failure, failure or resilience. What does culture mean to cybersecurity, though? Is it security awareness? Is it the collaboration between security teams and other functional teams? Is it the willingness of people to report potential security incidents? Maybe it's about teams being aware of security requirements while building new things.
Yes. It's all of those things. It's more than that as well.
This article will explore what a positive cybersecurity culture looks like, how to contribute to it regardless of your level, and some of its significant benefits. After all, "culture eats strategy for breakfast," as the late Peter Drucker once said.
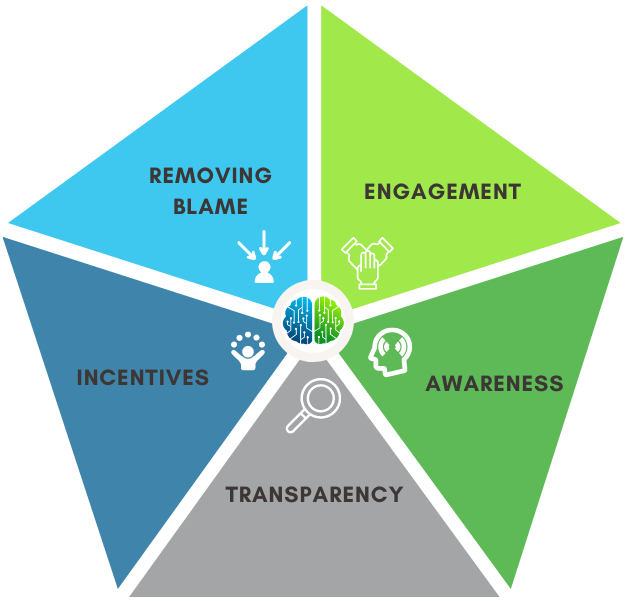
The 5 Pillars of a Strong Cybersecurity Culture
Talk of cybersecurity culture often conjures discussion around specific areas of work, security awareness training, or incident reporting, for example. However, I believe it's much bigger and more important than that. Investing in a culture that embraces cybersecurity is powerful. Further, it's paradigm shaking when cybersecurity takes the opportunity to lean in and positively contribute to an organization's culture and mission.
The shift from where all ideas and progress go to being told "no," is now out in front, helping, enabling, encouraging, and supporting.
There are five key ingredients or pillars of a strong cybersecurity culture. We're going to break each of these down in detail.
(Removing) Blame
Nobody wants to be thrown under the metaphorical bus when something goes wrong. People will be less willing to reach out and report issues if they feel there might be some form of retribution to follow. Anybody in the security organization can lead by example here. When something goes wrong, I encourage you to focus on the root issue and the circumstances that might have contributed to the problem instead of pointing the finger at who did what.
Stay mindful that anyone can make a mistake at any time. Stay away from backlash when people engage with the security team. Every team member must hold one another accountable for this particular issue. Moving away from a finger-pointing culture is not a CISO issue alone. The same goes for those working on the technical front lines.
A team that points fingers will gain a reputation even if it's only 1-2 members. That reputation is going to be very hard to shake over time. It's also hard to build trust and invite others in if the security team lays problems at others' feet.
Who can blame them?
Security teams can throw blame around for a lot of things. Perhaps it's for vulnerabilities that were found may get blamed on the developer who introduced them. Delays are blamed on the slowness of another team. Lack of budget may get blamed on executive peers or the finance team. Shifting priorities may get blamed on a sales or marketing team that is iterating on a go-to-market strategy.
Is it helpful anywhere? Is it moving your culture forward in a positive sense? My guess is probably not.
Take an internal inventory of your team's chatter to identify any places where there might be finger-pointing. Then, take steps to start setting a tone of a blameless culture and hold one another accountable to this effect.
Transparency
Transparency can be a sensitive topic in the field of cybersecurity. The work we do is sensitive and sometimes secretive. So shouldn't we be keeping sensitive things secret?
I'm not saying you should post your crown jewels on the internet. To me, transparency around investing in culture is about being open and honest about the team's goals, processes, and decisions. It's about actively seeking feedback from stakeholders to improve continuously. It's about making communications and meetings open whenever and wherever possible. You can invest in transparency in so many ways. These are a few of my favorites:
- Clear and open communication: Communicate the team's goals, processes, and decisions to stakeholders, including technical and non-technical information.
- Regular reporting: Regularly report on the team's progress, achievements, and challenges, and be transparent about areas for improvement. Signaling your team's intentions for future work and projects is an excellent opportunity to invite feedback.
- Open feedback loops: Encourage and facilitate open and honest feedback from stakeholders at any level, and be willing to listen to and act on that feedback. Feedback could be dedicated listening sessions, retrospectives, pulse surveys, or post-service touchpoints.
- Sharing information about significant events: Share information about security incidents and breaches and the steps taken to prevent similar incidents. Avoid the lame-duck empty messaging often used, like "our organization takes security and privacy very seriously...blah, blah. Instead, make it real and make it matter.
Transparency builds trust. Being intentionally transparent as a team helps reinforce this across the culture, which will have other benefits, such as increased collaboration and continuous improvement.
Take an inventory of your team's messaging, whether it's documentation, slack channels, or something else, and make a dedicated effort to convert them to a more transparent stance, such as public to anyone inside your organization.
Awareness
Awareness is more expansive than people understanding how to spot phishing emails or developers understanding how to write secure code. It includes those things but is not only those things.
Awareness is about the spread of knowledge and then contextualizing it to someone's day-to-For example, different people have different security needs in an organization.
- Software developers must understand the importance of dependency hygiene and safe coding practices.
- A Secretary needs to understand the nuances of spotting very targeted social engineering.
- HR and people operations teams need to know how to protect and safely use the sensitive yet specific applications they use.
- IT Administrators need to understand what it means
- Employees (and contractors if that's applicable in your organization) should understand how to engage the security team to disclose suspicious activity or report a breach.
This list could go on for way more than five bullet points. But hopefully, you get the point.
Security teams should not expect people to know everything, though, try as we might. We don't even know everything there is to know about security, so we can't pass that expectation along to others. It's too dynamic, and at the same time, it's too subtle.
So awareness then is also about ensuring people know how and where to go to stay in touch.
Take something in your spectrum of security awareness messaging and contextualize it to a specific role, team, or person. Then reach out and seek feedback on your work. Rinse and repeat.
Engagement
Engaging other teams means actively seeking out opportunities to do outreach, collaborate, and communicate with others. Generally, engagement with stakeholders is intended to connect and enhance the organization's overall security posture. This particular pillar is possibly one of my favorite elements of building security culture, making myself accessible to the non-security teams around me, and starting conversations.
Here are some specific ways to proactively engage others:
- Invest in relationship building: Take the time to get to know people on teams other than your own. Building a solid relationship includes understanding their goals, needs, and challenges. This comes with time; a strong relationship will not be built overnight.
- Share freely and proactively: Share information and knowledge about security threats, best practices, and the latest security technologies. Sharing can happen through presentations, reports, or regular updates. You might also share tools or interesting articles you read in non-security channels. Think about #engineering and #ops as your new water coolers.
- Plan and problem-solve together: Invite others to share their perspectives when planning and big cross-cutting problem-solving. That togetherness can be beneficial after a security incident.
- Cross-train with other teams: Look for opportunities to attend training sessions with different groups centered on technical skills development or relationship building. The benefit is togetherness.
- Encourage and invite feedback: Provide ample opportunities to consistently ask for input from others. The security team should ideally be open to others' perspectives on security issues or how security impacts their work.
Engagement connects you and your security team with others. A connected organization is more resilient than an organization with fragile organization and communication silos.
Set up some time this week with somebody from another team and ask them to share their honest perspective on the security program, how it could improve, and where they could get help. Then...listen.
Incentives
Merriam defines an incentive as "something that incites or has a tendency to incite to determination or action." Incentives in cybersecurity and culture change can come in many forms, the efficacy of which may heavily depend on your organization, its existing culture, your budget, and other resources (time, people, etc.) you have at your disposal.
At the cheap and easy end of the spectrum, it's a public shout-out to a person or a team for doing something that reinforces cybersecurity. Recognition and positive reinforcement can go a long way. For example, at a former employer, I started a program called the "human firewall award," where every month, we spotlighted a person who had an outstanding engagement with security, a phishing report that detailed why they thought it might be phishing, whether they engaged with it, and then spreading potential news in our company slack, for example. We passed this physical award to somebody new to display on their desk each month.

There are so many ways of providing positive reinforcement that could be delivered in a personalized message or group chat/email:
- What you did, made this organization safer today, and we are so appreciative.
- We wouldn't have been able to identify that phishing attempt so quickly if it wasn't for you reporting it.
- Wow, thank you for catching that bug and, even better, for fixing it; our scanner was not finding that.
Some organizations may have the resources to introduce small gifts into the workplace as an incentive. For example, a gift might be a gift card for coffee, a challenge coin, or a t-shirt. It doesn't have to be large, but it should be meaningful.
Recognizing an entire team for an effort can also be a powerful incentive. You can take the same concept of gifts or awards and apply them to teams with the most robust security posture. You could define it however you choose for the sake of engagement, the fastest mean time to remediate, the most coverage of mature security practices,
Get creative with it.
Create one today if your organization doesn't have a kudos channel or means of doing shout-outs for good work. Then, commit to following up on things that are going well with public recognition.
Concluding Thoughts
Despite being a technical field, cybersecurity is heavily steeped in people and culture. Creating and investing in a strong culture can elevate the work you're trying to do in cybersecurity. More engagement with your stakeholders, more friendly interactions, a more aware workforce, and so on. This article broke down five pillars of a strong cybersecurity culture and ways to start putting things into practice to improve yours.


